
Kasey Cromer, Netlok | February 23, 2026
Executive Summary
Your employees rely on dozens of mobile and desktop apps every day to collaborate, communicate, and get work done. Attackers know this. In 2025, 83% of organizations surveyed experienced app-targeted attacks, up from 65% the year before (Digital.ai). Infostealers harvested 1.8 billion credentials (DeepStrike). Importantly, 80% of employees now use apps that IT never approved (Microsoft).
The result is an authentication crisis hiding in plain sight. Every app is an entry point. Every login is a potential vulnerability. And most security tools still focus on protecting internal assets while leaving mobile, web, and desktop apps exposed to attacks that happen outside the corporate firewall.
Here’s what security leaders need to understand:
1) Apps have become the dominant attack surface. Credential theft, OAuth token abuse, and infostealer malware all target the authentication layer that apps rely on.
2) Shadow IT is no longer the exception. With employees adopting unsanctioned apps and AI tools without oversight, organizations face authentication blind spots they cannot control.
3) Photolok Passwordless IdP addresses this gap by providing identity verification that works across apps, integrates with existing systems like Okta Workforce, and gives attackers nothing to steal, intercept, or replay.
The App Attack Surface in 2026
Apps and identity now form a single, concentrated attack surface. The chart below shows how these risks converge—app-targeted attacks climbing year over year, most employees on unsanctioned apps, and a majority of SaaS accounts still running without MFA, while nearly half of attacks trace back to shadow IT.
App-Based Security Threats (2024-2025)
Apps and identity are now the primary enterprise attack surface
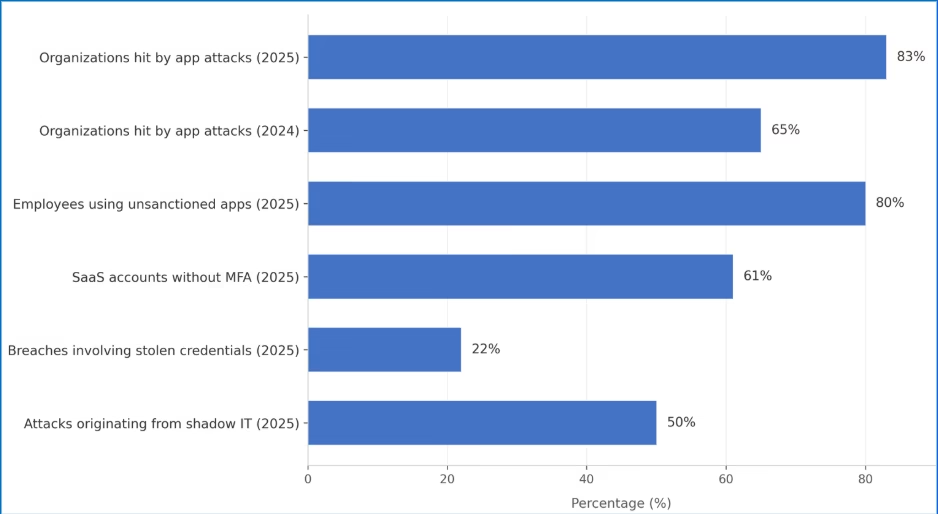
Source: Digital.ai, Verizon DBIR, Microsoft, SaaS Alerts, Zluri/analyst estimates (2025 data)
The rest of this article unpacks what those numbers mean operationally for your security program.
Mobile devices are no longer just communication tools. They are central to payments, identity verification, healthcare, and enterprise processes. Desktop apps handle everything from financial transactions to customer data. Each app authenticates users, often multiple times per day, creating thousands of potential entry points for attackers.
Credential Theft at Scale
The numbers are hard to ignore. DeepStrike’s 2025 analysis found that infostealer malware harvested 1.8 billion credentials in 2025 alone. These aren’t theoretical risks. Infostealers now operate as Malware-as-a-Service, with attackers deploying them through phishing emails, malicious apps, and compromised websites.
In June 2025, researchers discovered what may be the largest credential exposure in history: roughly 16 billion login credentials compiled from infostealer logs, phishing kits, and prior breaches. The Verizon 2025 DBIR found that credential stuffing now accounts for 19% of all authentication attempts at the mid-level companies, rising to 25% at large organizations.
Mobile Apps as Attack Vectors
Mobile phishing has become significantly more effective than email. Spacelift’s 2026 research found that SMS phishing achieves click rates of 19% to 36%, compared to just 2% to 4% for email—up to nine times more effective. Mobile screens unintentionally hide full URLs and security indicators, making phishing links harder to detect (Spacelift). Users move quickly on their phones. And attackers exploit urgency with messages like “Your account is locked” or “Your package is arriving.”
CompareCheapSSL reports that 63% of mobile users received a phishing SMS in the last 90 days. Malicious apps compound the problem. Researchers detected over 100,000 fake apps across major app stores in 2025 (CompareCheapSSL). These apps steal credentials, harvest data, and install backdoors that persist even after removal. And nearly a quarter of enterprise devices now host apps installed outside official app stores that bypass app store security entirely.
Shadow IT and Unsanctioned Apps
Employees aren’t being malicious—they’re trying to be productive. But every unsanctioned app introduces authentication touchpoints that IT cannot see or secure. IBM’s 2025 research found that the average enterprise uses 975 cloud services, but IT departments officially track only 108. The vast majority remain invisible to security teams. Analyst reports from Zluri and CloudEagle peg average shadow IT remediation costs above $4.2 million. Gartner predicts that by 2027, 75% of employees will use technology outside IT oversight. The perimeter has not just expanded. It has dissolved.
Shadow AI: The Newest Blind Spot
Generative AI has created a new category of shadow IT. Employees across departments use ChatGPT, Claude, DeepSeek, and other AI tools to write code, summarize data, and automate workflows. Many do so without IT approval or oversight.
Komprise’s 2025 survey of IT executives found that 90% are concerned about shadow AI from a privacy and security standpoint. Nearly 80% have already experienced negative AI-related data incidents, and 13% report those incidents caused financial, customer, or reputational harm. Between 31% and 38% of AI-using employees enter sensitive work data into AI tools. Once that data leaves the organization, it may be logged, cached, or used for model retraining—permanently outside organizational control.
The IBM Cost of a Data Breach Report found that shadow AI incidents add roughly $670,000 to the average breach cost, pushing totals to $5.11 million versus the $4.44 million global average.
This is why identity-layer controls matter: you cannot control which AI tools employees actually use, but you can govern how they authenticate to reach sensitive data in the first place.
OAuth and Third-Party App Risk
Modern apps connect to enterprise systems through OAuth tokens, API keys, and session credentials. All of these grant access without requiring passwords at each interaction. If any of these are stolen from an unapproved app, attackers can impersonate legitimate users and access corporate data without triggering authentication alerts.
Obsidian Security reports that the biggest SaaS breach of 2025 started with a compromised third-party app exploiting OAuth tokens—with a blast radius 10x greater than direct infiltration. More than 80% of apps are unfederated behind the identity provider, meaning they operate outside SSO and MFA policies. These gaps create direct paths for attackers.
Why Traditional Authentication Is Failing
These weaknesses show up first at the app layer, where users are authenticating dozens of times per day. Unfederated apps require their own passwords and credentials, separate from corporate SSO, multiplying the number of authentication touchpoints attackers can target. Every attack we’ve described exploits the same fundamental weakness: authentication systems that can be observed, intercepted, or replicated.
Passwords remain the weakest link—the majority of hacking-related breaches still involve compromised credentials somewhere in the attack chain. AI and machine learning can now generate sophisticated phishing schemes and crack passwords far more efficiently than ever before.
SMS codes can be intercepted through SIM swapping, which the FBI’s Internet Crime Complaint Center (IC3) says led to nearly 1,000 complaints and about $26 million in reported losses in 2024 alone in the U.S. Custom vishing kits can intercept one-time passwords in real time while attackers are on the phone with victims, turning a single SIM swap into a high-impact account takeover.
Passkeys offer better phishing resistance than passwords, but the private key is often stored in device managers. If the device or manager is breached, it becomes a single point of compromise.
Biometrics add convenience, but deepfakes, voice clones, and synthetic identity attacks are making biometric spoofing significantly easier. Once compromised, biometrics cannot be reset.
Why Photolok Addresses the 2026 App Security Landscape
Photolok is not another app. It is a Passwordless Identity Provider (IdP) that functions as the front door for your apps. It works with your existing systems, including Okta Workforce and other identity platforms. As an identity provider, Photolok verifies who users are before granting access to any application. By replacing passwords at this identity layer, Photolok secures authentication across every app your employees use, whether sanctioned or not. The apps themselves never see or store credentials. They simply trust Photolok’s verification.
Steganographic photo-based authentication with AES-256 encryption: Photolok’s patented system embeds encrypted codes within photos, generating a new AES-256 code every session. Users authenticate by selecting from randomized photos only they would recognize—creating verification that cannot be observed and replayed like a password, intercepted like an SMS code, or deepfaked like a biometric.
Randomized recognition challenges: Because photos are randomized every session, AI and machine learning tools have no pattern to learn and no credential to harvest. Unlike passwords or biometrics, there is no static data for attackers to brute-force or simulate.
Device approval and fingerprinting: Users control which devices can access their account. Combined with device fingerprinting, this blocks unauthorized access attempts even if attackers somehow obtain login information.
Situational security protection: Photolok is the only login method with built-in protection for high-risk situations. The Duress Photo acts as a visual silent alarm when users are coerced—whether through social engineering, insider pressure, or threats. The 1-Time Photo protects against shoulder surfing by removing itself after a single use.
User-friendly and cost-effective: Point-and-click navigation with no passwords to remember or reset. This eliminates one of the most common IT support burdens while leveraging the brain’s natural picture-superiority effect for faster, more intuitive authentication.
What Security Leaders Should Do Now
1. Map your app attack surface. Identify all mobile, desktop, and SaaS apps that employees use—sanctioned and unsanctioned. Determine which apps are federated behind your IdP and which operate outside your authentication controls.
2. Assume credentials have been compromised. With 1.8 billion credentials harvested in 2025 alone, the question is not whether your employees’ credentials are in attacker databases, but how you protect authentication when they are. Move beyond passwords and SMS codes for high-risk access.
3. Address shadow IT at the identity layer realistically. You cannot control which apps employees actually use, but you can govern how they authenticate. Solutions like Photolok Passwordless IdP secure the identity layer regardless of what apps sit on top of it.
4. Establish AI governance before shadow AI becomes a breach. Create clear policies for which AI tools are approved and how sensitive data should be handled. Monitor for unauthorized AI usage and provide approved alternatives that meet security requirements.
5. Audit third-party app connections and integrations. Review which apps have access to your enterprise systems through OAuth tokens, API keys, and session credentials. Revoke unnecessary permissions and monitor for anomalous usage.
The Bottom Line
Your workforce runs on apps. So do attackers. Every mobile app, desktop application, and SaaS tool is an authentication touchpoint that attackers can exploit. And with 80% of employees using unsanctioned apps, you cannot secure what you cannot see.
The answer is not to fight the app explosion—it is to secure the identity layer that apps depend on. Photolok Passwordless IdP secures authentication across your app ecosystem, integrates with systems like Okta Workforce, and gives attackers nothing to steal, intercept, or replay.
These attacks show up as unplanned losses, regulatory scrutiny, and board-level questions about why known identity weaknesses were not addressed sooner. The tools exist. The question is whether your organization will deploy them before or after the breach.
Want to see how Photolok can help secure your organization’s app ecosystem?
Request Your Personalized Demo
About the Author
Kasey Cromer is Director of Customer Experience at Netlok.
Sources
[1] Digital.ai. “2025 Application Security Threat Report.” digital.ai
[2] DeepStrike. “Stealer Log Statistics 2025.” deepstrike.io
[3] Verizon. “2025 Data Breach Investigations Report.” verizon.com
[4] Spacelift. “70 Social Engineering Statistics for 2026.” spacelift.io
[5] CompareCheapSSL. “Mobile Security Statistics 2026.” comparecheapssl.com
[6] Nudge Security. “Shadow IT Discovery Guide” (citing Microsoft). nudgesecurity.com
[7] Fidelis Security. “Shadow IT Risks and Detection” (citing IBM). fidelissecurity.com
[8] Zluri. “Shadow IT Statistics 2025.” zluri.com
[9] CloudEagle. “Risks of Shadow IT.” cloudeagle.ai
[10] CIO. “Shadow AI: Hidden Agents Beyond Governance.” cio.com
[11] Bright Defense. “Data Breach Statistics 2026” (citing IBM). brightdefense.com
[12] Obsidian Security. “What Is Shadow SaaS?” obsidiansecurity.com
[13] GitProtect. “Cybersecurity Statistics 2026” (citing SaaS Alerts). gitprotect.io
[14] FBI Internet Crime Complaint Center. “2024 Internet Crime Report.” ic3.gov
[15] Netlok. “How Photolok Works.” netlok.com

Protecting the Person, Not Just the Account
Kasey Cromer, Netlok | March 31, 2026 Executive Summary Traditional authentication was designed to a[...more]

Why Passwords and Biometrics are Failing in 2026
Kasey Cromer, Netlok | March 18, 2026 Executive Summary The identity and authe[...more]

Pig Butchering Has Gone Big Time. Your Identity Layer Has to Catch Up.
Kasey Cromer, Netlok | February 28, 2026 Executive Summary “Pig butchering” refers[...more]

Your Workforce Runs on Apps. So Do Attackers.
Kasey Cromer, Netlok | February 23, 2026 Executive Summary Your employees rely on dozens of mo[...more]

When AI Becomes the Con Artist
Kasey Cromer, Netlok | February 12, 2026 Executive Summary Social engineering has always explo[...more]

Agentic AI in the Enterprise: The Security Guide Nobody Gave You
Kasey Cromer, Netlok | January 27, 2026 Executive Summary Autonomous AI agents are now executing cod[...more]

Workplace Security in 2026: When AI, Insiders, and Remote Work Collide
Kasey Cromer, Netlok | January 15, 2026 Executive Summary The uncomfortable truth about workplace se[...more]

How Insider Threats Bypass Security: Why Traditional Authentication Fails in the AI Era
Kasey Cromer, Netlok | January 5, 2026 Executive Summary Insider threats now cost an average of $17.[...more]

Authentication at a Crossroads: Preparing for the AI-Powered Threat Landscape of 2026 and Beyond
Kasey Cromer, Netlok | December 4, 2025 Series Recap Part 1 (November 14, 2025) took a deeper dive i[...more]